Amazon.it: Windows APT Warfare: Identify and prevent Windows APT attacks effectively - Ma, Sheng-Hao, Chang, Ziv, Maggi, Federico - Libri

Amazon | Meta-Logics and Logic Programming | Apt, Krzysztof R., Turini, Franco | Human Vision & Language Systems

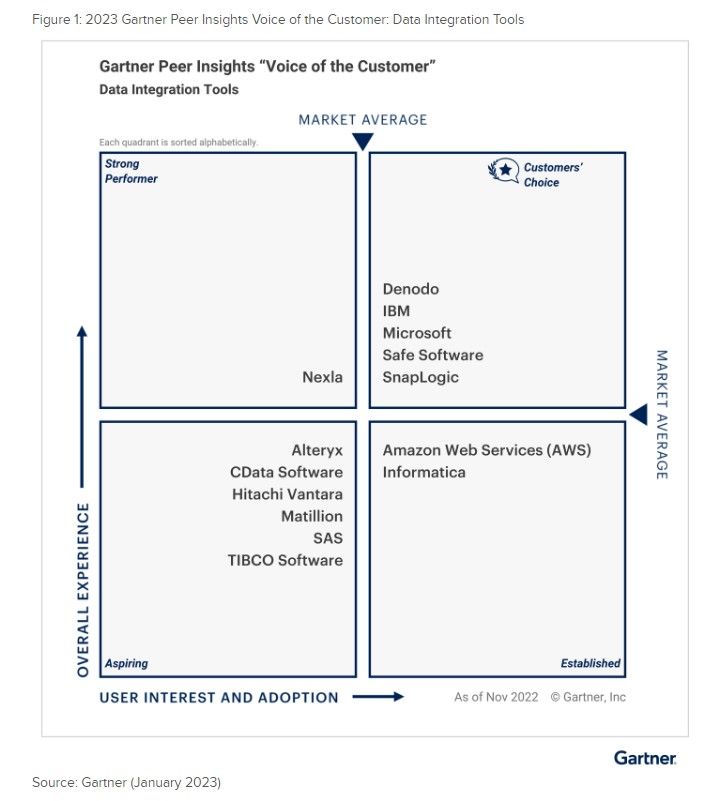
Create Amazon SageMaker model building pipelines and deploy R models using RStudio on Amazon SageMaker | Data Integration

Amazon.it: Windows APT Warfare: Identify and prevent Windows APT attacks effectively - Ma, Sheng-Hao, Chang, Ziv, Maggi, Federico - Libri

Amazon.it: From CIA to APT: An Introduction to Cyber Security - Amoroso, Edward G., Amoroso, Matthew E. - Libri

Apt a 1,5 m 3m 5m SCSI20 SCSI 20 Pin Cavo dei Dati del terminale Maschile CN. Tipo Cavo del connettore della Scheda di acquisizione (Color : 1.5m) : Amazon.it: Informatica